The QUATTRO is one of the most flexible, efficient and compact lasers on the market. Many metal working companies have a large number of components to manufacture but only need to produce one or two at a time. Ease of use, plus low operating costs make the QUATTRO the ideal solution for low volumes, without forgoing precision and quality.
This machine is no longer available.
Find the laser machine that suits your needs
Disclaimer: This article is for educational purposes only. Always consult legal counsel before deploying offensive countermeasures in a production environment.
For the security analyst tired of playing whack-a-mole, for the incident responder watching an attacker leisurely browse your file shares, and for the blue team lead who wants to fight back—this PDF is your playbook. The art of active defense is the future. Begin studying it today. Search for “SANS FOR528 Active Defense Syllabus” to find the official course materials referencing the PDF. Then, deploy one honeytoken this week. That single act moves you from passive defender to active practitioner. offensive countermeasures the art of active defense pdf
In the modern cybersecurity landscape, the traditional mantra of “prevent, detect, respond” is no longer sufficient. Attackers have the advantage of time, stealth, and initiative. In response, a controversial yet increasingly vital discipline has emerged: Offensive Countermeasures (OCM) . For security professionals seeking to master this shift, one document has become a seminal text: “Offensive Countermeasures: The Art of Active Defense.” This article serves as a deep dive into the concepts of that PDF, exploring why it has become a must-read for red, blue, and purple teams alike. What Are Offensive Countermeasures? (Beyond the PDF) Before locating or studying the PDF, one must understand the core definition. Offensive Countermeasures are proactive, aggressive actions taken against an attacker inside your network —before they exfiltrate data. This is not "hacking back" (which is legally murky and involves leaving your network). Instead, OCM focuses on active defense inside your own digital perimeter. Disclaimer: This article is for educational purposes only
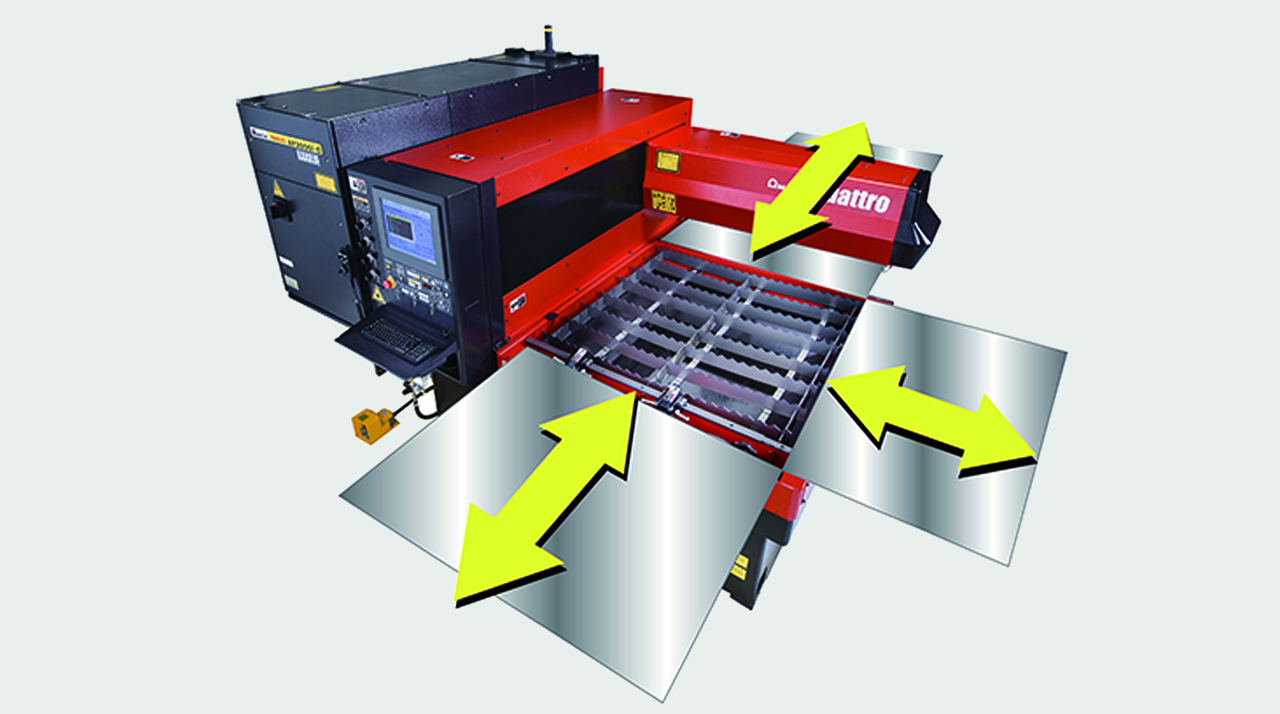
FULL ACCESS TO THE CUTTING AREA:
The three accessible sides of the QUATTRO laser facilitate sheet metal loading and unloading. Large-sized sheets which are bigger than the work area can also be processed, repositioning them manually.

COMPACT STRUCTURE:
With a footprint of just 6.4 m2, the QUATTRO is AMADA's smallest laser. The oscillator and numerical control are contained within the machine to maintain its extremely compact size.

DIVERSIFIED PROCESSING:
With the QUATTRO, not only sheet metal but rectangular and square tubes can be processed, providing even greater flexibility. (Option)

| QUATTRO | QUATTRO | |
|---|---|---|
| Laser power (W) | 1000 | 2500 |
| Machine type | CO₂ flying optic laser | CO₂ flying optic laser |
| Working range X x Y (mm) | 1250 x 1250 | 1250 x 1250 |
| Working range Z-axis (mm) | 100 | 100 |
| Table loading weight (kg) | 80 | 160 |
Material thickness (max.)*: | ||
| - Mild steel (mm) | 6 | 12 |
| - Stainless steel (mm) | 2 | 5 |
| - Aluminium (mm) | 1 | 4 |
Dimensions: | ||
| Length (mm) | 2900 | 2950 |
| Width (mm) | 2450 | 2450 |
| Height (mm) | 2160 | 2160 |
| Weight (kg) | 3750 | 4150 |
* Maximum thickness value depends on material quality and environmental conditions
Technical data can vary depending on configuration / options
Please contact us for more details and options or download our brochure

For your safe use.
Be sure to read the user manual carefully before use.
When using this product, appropriate personal protection equipment must be used.

Laser class 1 when operated in accordance to EN 60825-1
Disclaimer: This article is for educational purposes only. Always consult legal counsel before deploying offensive countermeasures in a production environment.
For the security analyst tired of playing whack-a-mole, for the incident responder watching an attacker leisurely browse your file shares, and for the blue team lead who wants to fight back—this PDF is your playbook. The art of active defense is the future. Begin studying it today. Search for “SANS FOR528 Active Defense Syllabus” to find the official course materials referencing the PDF. Then, deploy one honeytoken this week. That single act moves you from passive defender to active practitioner.
In the modern cybersecurity landscape, the traditional mantra of “prevent, detect, respond” is no longer sufficient. Attackers have the advantage of time, stealth, and initiative. In response, a controversial yet increasingly vital discipline has emerged: Offensive Countermeasures (OCM) . For security professionals seeking to master this shift, one document has become a seminal text: “Offensive Countermeasures: The Art of Active Defense.” This article serves as a deep dive into the concepts of that PDF, exploring why it has become a must-read for red, blue, and purple teams alike. What Are Offensive Countermeasures? (Beyond the PDF) Before locating or studying the PDF, one must understand the core definition. Offensive Countermeasures are proactive, aggressive actions taken against an attacker inside your network —before they exfiltrate data. This is not "hacking back" (which is legally murky and involves leaving your network). Instead, OCM focuses on active defense inside your own digital perimeter.