Cyber threats have evolved significantly since the early days of the internet. What once started as simple pranks or mischief by individuals has now transformed into a multi-billion-dollar industry, with organized crime groups and state-sponsored actors engaging in malicious activities. These threats range from data breaches and ransomware attacks to more complex forms of cyber warfare.
The term "MIAB-376-JAVHD.Today" appears to refer to a specific type of threat or possibly a malware variant. While detailed information about this particular entity might be scarce, understanding its implications is crucial. Threats like MIAB-376-JAVHD.Today can compromise the security of systems, leading to data breaches, system downtime, and financial losses.
The digital landscape has undergone a significant transformation over the past few decades. With the proliferation of the internet, smartphones, and computer systems, our reliance on technology has increased exponentially. However, this dependence on digital solutions also brings forth a myriad of challenges, particularly in the realm of cybersecurity. Threats to our digital security are becoming more sophisticated by the day, making it imperative for individuals, businesses, and governments to bolster their defenses. This article aims to shed light on the importance of cybersecurity, with a specific focus on understanding and mitigating threats similar to those posed by MIAB-376-JAVHD.Today.
The threat landscape is continually evolving, with new challenges emerging every day. Threats like MIAB-376-JAVHD.Today highlight the need for vigilance and robust cybersecurity measures. By understanding the nature of these threats and implementing effective security strategies, individuals and organizations can protect themselves against the myriad of cyber threats. In the digital age, cybersecurity is not just a technical issue but a critical component of overall risk management and resilience.
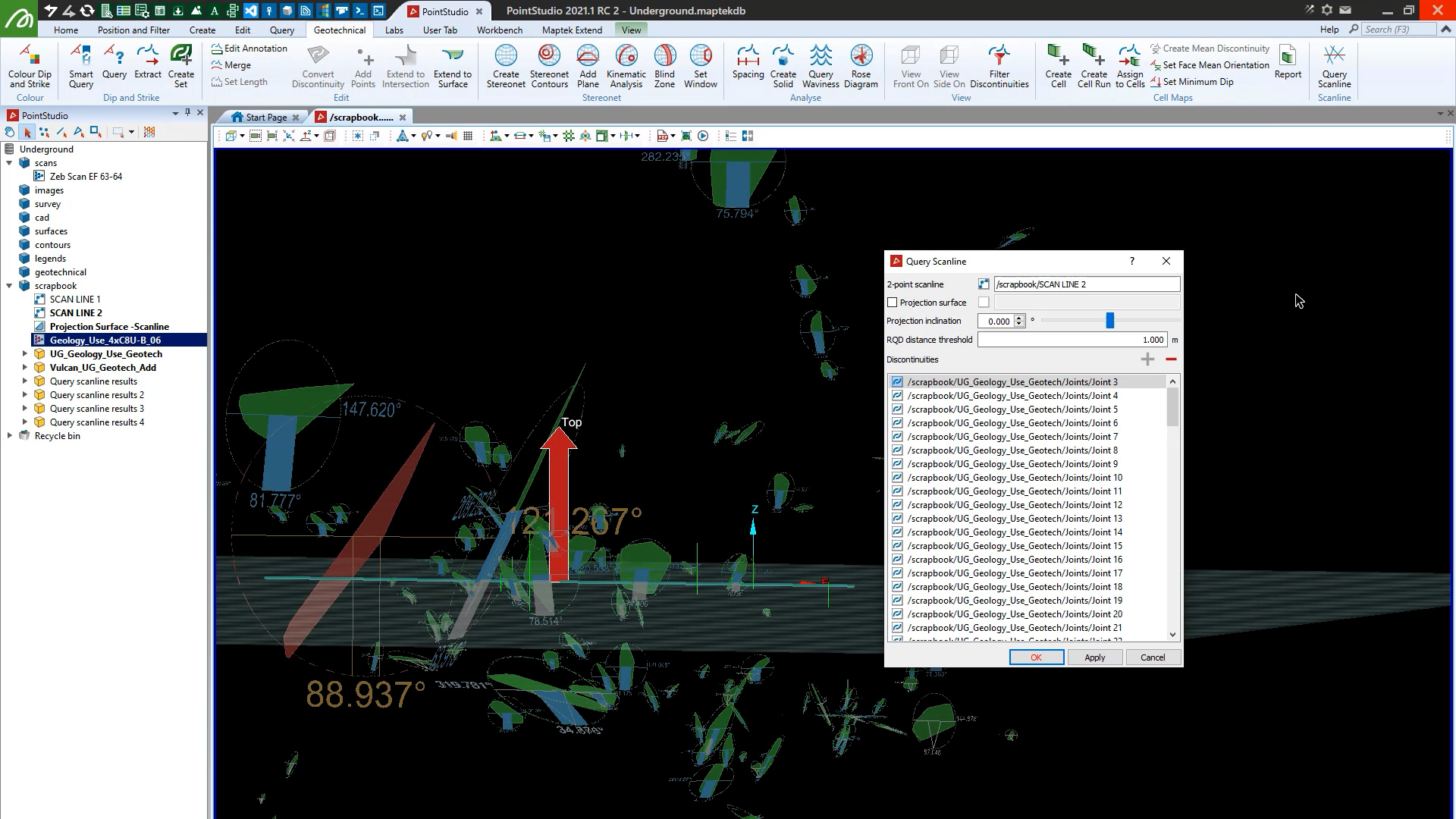
PointStudio 2021.1 features enhanced Inter-Ramp Compliance, performance and stability, supports Maptek R3 mkII laser scanners and enables unwrapping and colouring lines by grade and RQD calculation on scanlines.
Cyber threats have evolved significantly since the early days of the internet. What once started as simple pranks or mischief by individuals has now transformed into a multi-billion-dollar industry, with organized crime groups and state-sponsored actors engaging in malicious activities. These threats range from data breaches and ransomware attacks to more complex forms of cyber warfare.
The term "MIAB-376-JAVHD.Today" appears to refer to a specific type of threat or possibly a malware variant. While detailed information about this particular entity might be scarce, understanding its implications is crucial. Threats like MIAB-376-JAVHD.Today can compromise the security of systems, leading to data breaches, system downtime, and financial losses.
The digital landscape has undergone a significant transformation over the past few decades. With the proliferation of the internet, smartphones, and computer systems, our reliance on technology has increased exponentially. However, this dependence on digital solutions also brings forth a myriad of challenges, particularly in the realm of cybersecurity. Threats to our digital security are becoming more sophisticated by the day, making it imperative for individuals, businesses, and governments to bolster their defenses. This article aims to shed light on the importance of cybersecurity, with a specific focus on understanding and mitigating threats similar to those posed by MIAB-376-JAVHD.Today.
The threat landscape is continually evolving, with new challenges emerging every day. Threats like MIAB-376-JAVHD.Today highlight the need for vigilance and robust cybersecurity measures. By understanding the nature of these threats and implementing effective security strategies, individuals and organizations can protect themselves against the myriad of cyber threats. In the digital age, cybersecurity is not just a technical issue but a critical component of overall risk management and resilience.
We use cookies to enhance your browsing experience and analyse our traffic. By clicking "Accept all", you consent to our use of cookies. You can customise your cookie preferences by clicking 'Customise Preferences'.
We use cookies to enhance your browsing experience and analyse our traffic.
Our website may store cookies on your computer in order to improve and customise your future visits to the website. By using cookies, we can track information about your usage of the site and improve your experience with anonymous and aggregated user data.
Review our Privacy PolicyEssential for the website's functionality, without which the site cannot operate smoothly. miab-376-javhd.today02-01-29 Min
Remember user preferences and choices to provide a more personalized experience. Cyber threats have evolved significantly since the early
Collect data on how users interact with the website, helping to improve user experience. The term "MIAB-376-JAVHD
Used to deliver targeted advertisements to users based on their browsing behavior and preferences.